Finger Bending Biometrics — Smart Glove
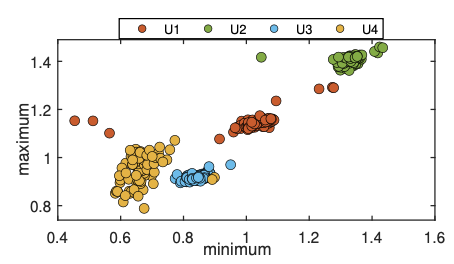
Key Findings - 2D embedding (PCA / t-SNE) of multi-finger flex features, colored by user
- Optional inset: same plot using single-finger vs multi-finger features
- Finger bending signals formed separable user-specific clusters, even when considering fingers that were not directly pressing keys.
- Typing induces coordinated, involuntary finger motion driven by neuromuscular coupling, meaning identity cues emerge from how fingers move together, not just from keypress timing or active fingers.
- Error rates are not sufficient for standalone authentication, and glove-based sensing introduces wearability and calibration constraints, positioning this modality best as a complementary signal rather than a replacement.
Gamified Wearable Data Collection — Smartwatch IMU
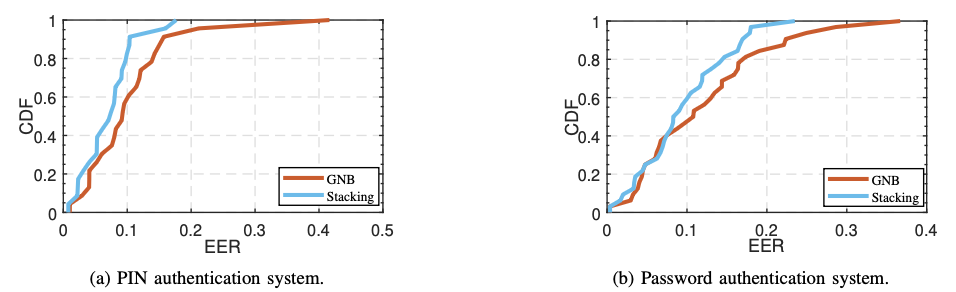
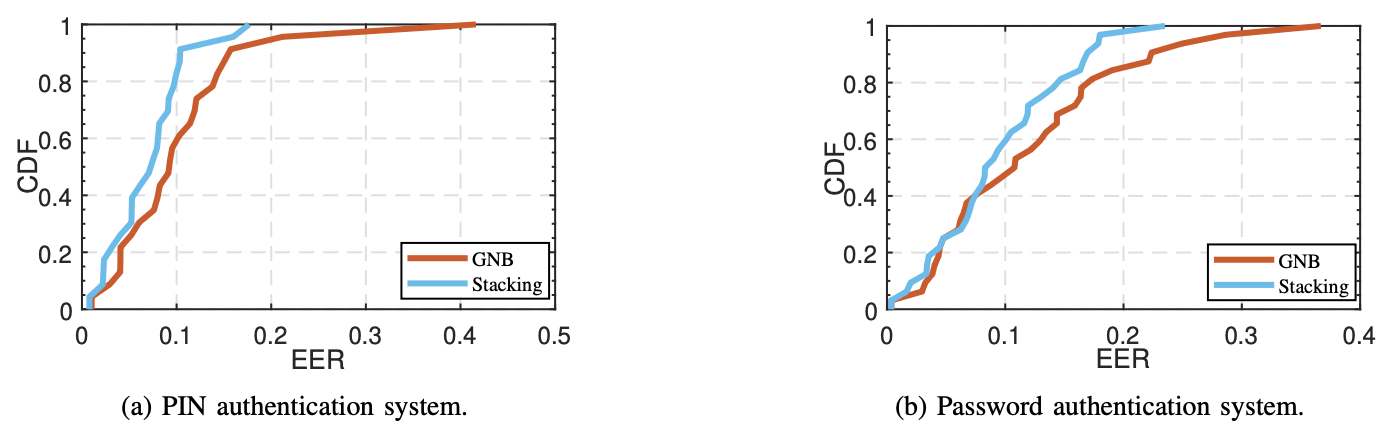
Key Findings - Trained on direct execution → tested on direct execution
- Trained on gamified execution → tested on direct execution
- Motion patterns collected during gameplay remained predictive of authentication patterns, though with measurable drift compared to directly executed inputs.
- Core motor habits persist across interaction contexts, allowing gamified tasks to preserve behavioral signatures even when user intent and attention differ.
- Gamification alters execution dynamics and lowers fidelity in some cases, while also introducing a new attack surface where benign-looking apps can covertly collect sensitive behavioral data.
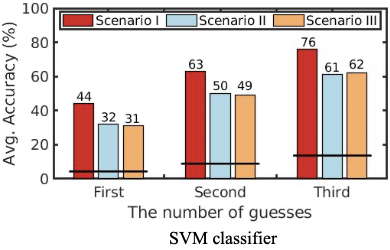
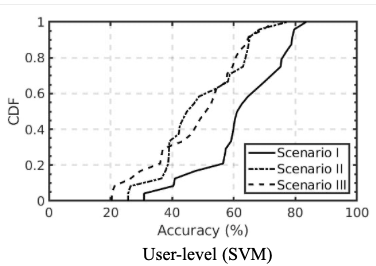
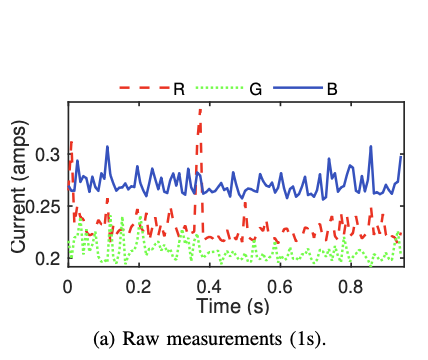
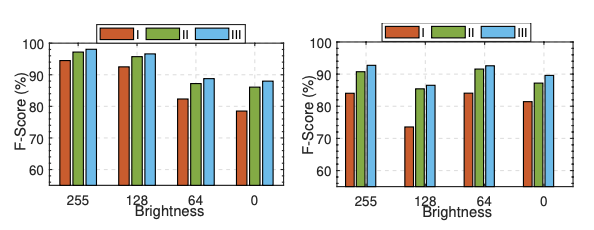
Power Side-Channel Video Inference — Charging Hubs
Key Findings - Videos could be identified with high accuracy from charging power traces alone, under realistic brightness, volume, and device conditions.
- Visual content drives structured brightness and color transitions on modern displays, which imprint stable spectral and entropy patterns onto power consumption observable at the charger.
- Attack effectiveness degrades at low brightness and across mismatched device models, indicating that inference relies on a combination of content structure and hardware characteristics, not a universal leakage channel.