2021
-
 On Finger Stretching and Bending Dynamics as a Biometric ModalitySraddhanjali Acharya, and Abdul Serwadda2021
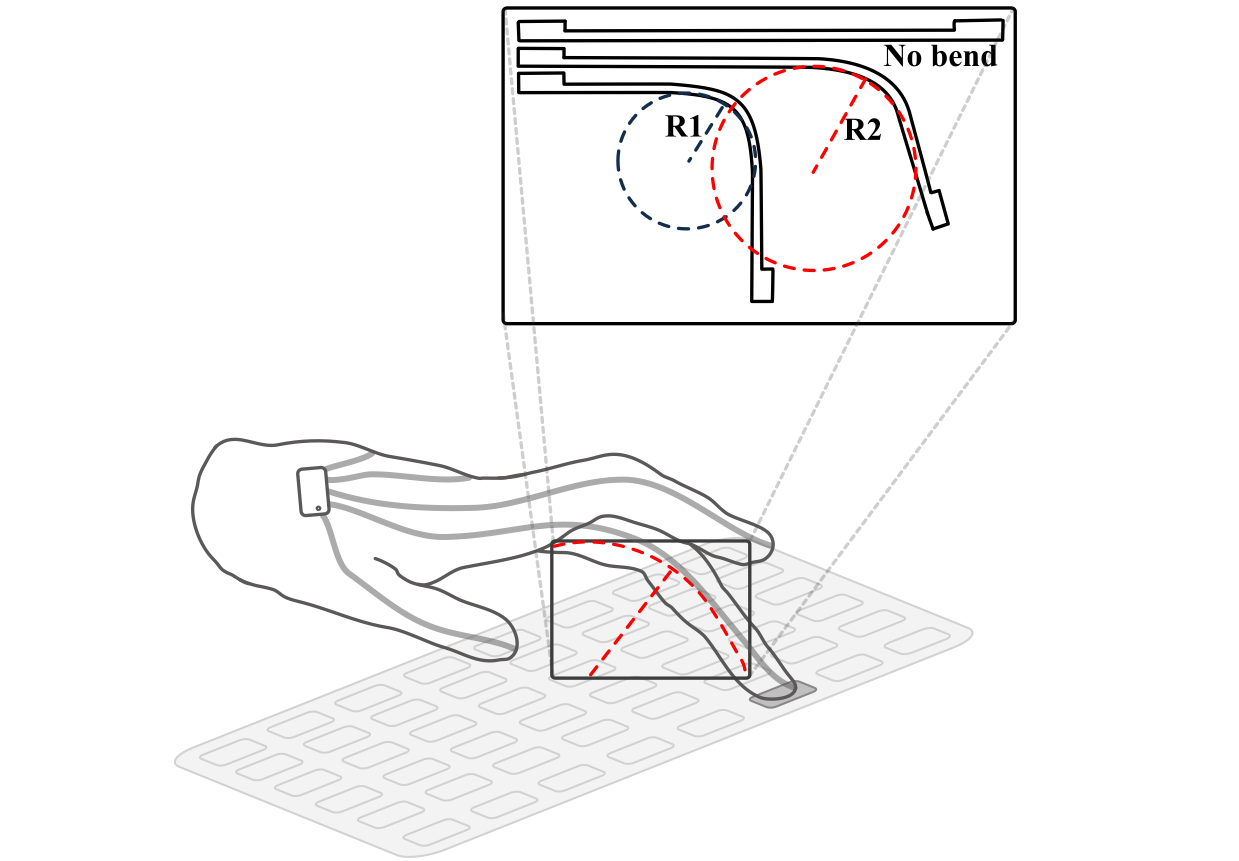
On Finger Stretching and Bending Dynamics as a Biometric ModalitySraddhanjali Acharya, and Abdul Serwadda2021Studies on the characterization of the dexterity of fingers and hands improve the understanding of how humans interact with computing devices. In this study, finger bending patterns captured by flex sensors worn on the fingers are characterized to build a biometric authentication system. The modality uses an array of resistive sensors fitted in a smart glove worn by users while typing. The study encompasses 55 users, 23 of them entered a 9-digit PIN on a laptop’s number pad, and 32 of them typed a 10-length alphanumeric password on the full-sized keyboard. The results demonstrate that the users are authenticated using features built from the flex sensors relating to their PIN and password with a mean EER score of 7.49% and 9.76%, respectively. We further assessed the potential of using individual fingers to authenticate users in both the biometric systems and found that even the fingers not used for typing ex- hibited discriminative patterns due to movement dynamics during the typing process. This assessment highlights the potential for designing lightweight biometric modalities utilizing dexterity and patterns based on fewer fingers.
-
 That phone charging hub knows your video playlist!Sraddhanjali Acharya, Abdul Serwadda, and Argenis V. Bilbao2021
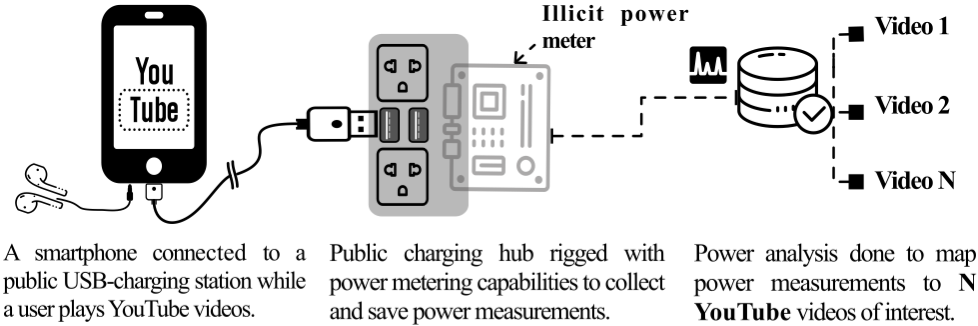
That phone charging hub knows your video playlist!Sraddhanjali Acharya, Abdul Serwadda, and Argenis V. Bilbao2021The rapid growth of smartphone usage has sparked a proliferation of public phone-charging hubs to cater to peoples’ growing charging needs. By virtue of being located in public spaces, however, these hubs have the potential to be manipulated by malicious actors who seek to use them as a vehicle to launch cyberattacks against the users of these hubs. In this paper, we show that if such a public charging hub is rigged with a power measurement circuitry, the power measurements could enable the inference of videos watched by the user on the phone. Using a playlist of 100 YouTube music videos, we show this kind of attack to classify the videos with an accuracy of up to 94.49%. We rigorously examine the dynamics of the attack using 5 different phone models, 16 screen brightness and volume configurations, and various training configurations and show it to be highly effective under a wide range of settings. Depending on the content of such videos, the profile of the target, and the attacker’s aims (e.g., government vs. private hacker), we argue that such an attack could have far-reaching privacy implications. The paper adds to the body of work highlighting power side-channels on computing devices as a potent threat to user privacy.
2019
-
 Gamification of wearable data collection: A tool for both friend and foeSraddhanjali Acharya, Richard Matovu, Abdul Serwadda, and Isaac Griswold-Steiner2019
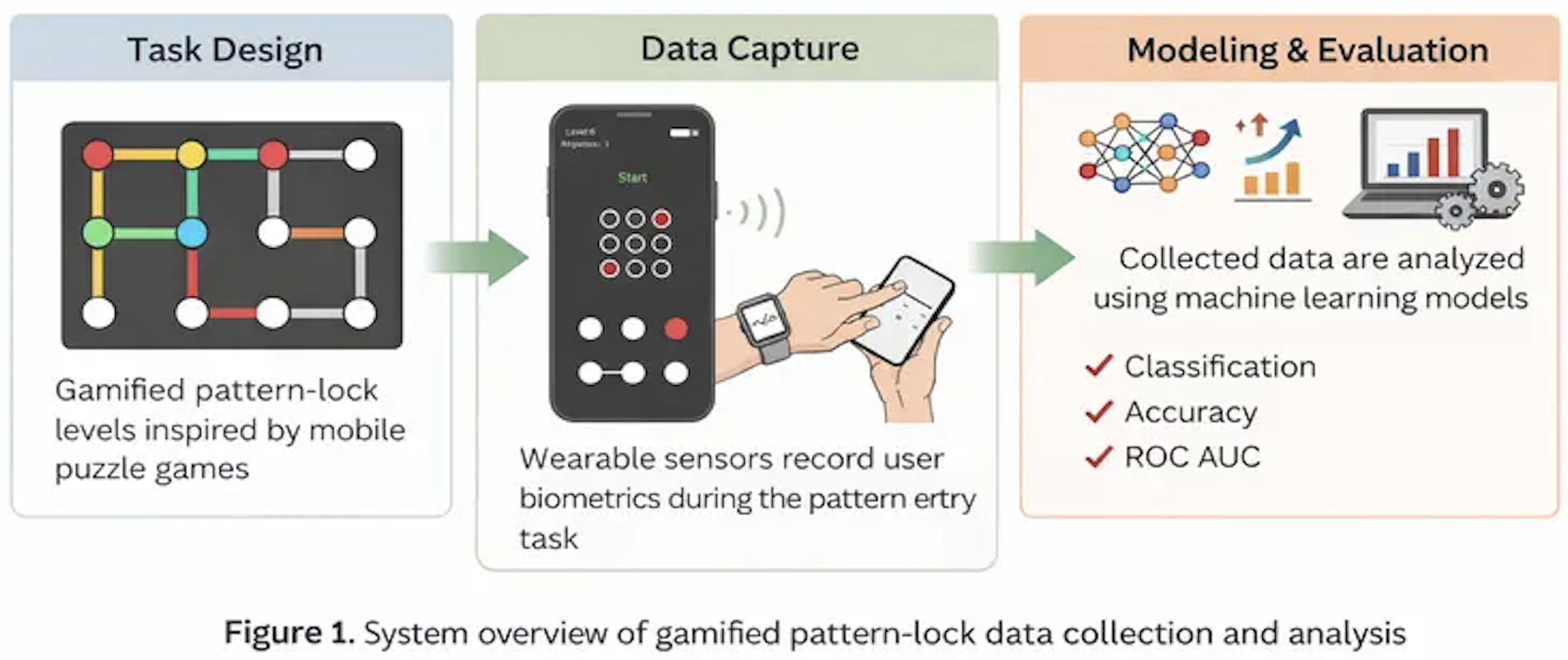
Gamification of wearable data collection: A tool for both friend and foeSraddhanjali Acharya, Richard Matovu, Abdul Serwadda, and Isaac Griswold-Steiner2019Games are designed to build on certain inherently reward centered aspects of our psychology. This encourages the user to keep playing and engaging in the entertainment for just a bit longer. In this paper we explore the way in which gamification can be used to benefit researchers aiming to collect large amounts of data from sometimes less than enthusiastically motivated participants. We also investigate the risks associated with such mechanisms for data collection and how malicious entities could use these same methods to trick users into exposing private information. Across several experiments used to measure the cross-applicable nature of the data we collected, we demonstrate that a gamified version of a data collection tool could be used to predict the pattern used to unlock a phone.